I. Introduction
BRICKSTORM is a Golang-based backdoor used by the Chinese state-sponsored group, UNC5221 (also known as UTA0178 and Red Dev 61), to quietly maintain long-term access to enterprise and government networks. It is a cross-platform threat that targets Windows, Linux, and BSD-based systems, with a particular focus on edge appliances and remote access infrastructure.
Identified by Mandiant (Google Cloud) in March 2025, this malware has been linked to multiple espionage incidents in the US, including attacks on law firms, Software-as-a-Service (SaaS) providers (companies that offer software applications over the internet), and technology companies.
What makes BRICKSTORM so dangerous is the emphasis on stealth and persistence. Mandiant uncovered one case that revealed BRICKSTORM included a built-in “delay” timer that waited for a specific (hardcoded) date before contacting its command-and-control server, which meant that the threat actor was actively monitoring and capable of adapting their tactics to maintain persistence. Mandiant averages the dwell time for BRICKSTORM malware to be 393 days before detection, highlighting just how effective this backdoor malware can be at evading detection.
Once compromised, BRICKSTORM threat actors will not only compromise the entire environment of their target organization but also the organization’s connections, thereby expanding their attack surface and reaching beyond the initial target.
This advisory will cover what BRICKSTORM is, its targets, Tactics Techniques & Procedures, tools and services used, Indicators of Compromise, as well as mitigation strategies to protect against BRICKSTORM.
II. Target
Legal Services / Law Firms
U.S. law firms and legal services organizations, especially those specializing in mergers and acquisitions, international trade, and government contracting, are primary targets for BRICKSTORM, as these areas provide access to sensitive information about U.S. economic and national security matters [12]. These firms are a valuable source of private/internal communications, transaction records, and trade intelligence that provide strategic insight into U.S. economic and national security matters. The motivation behind these attacks is primarily espionage, as the adversary seeks to obtain privileged emails, negotiation strategies, and other confidential materials that can be used for political or trade advantage. Reporting shows that these campaigns are not short-term, financially driven operations, but long-term intelligence collection efforts that remain active for extended periods, often through persistent access in internal document systems and email servers.
Technology Firms / Intellectual Property-Rich Companies
Technology firms, software vendors, and R&D organizations attract BRICKSTORM due to their proprietary source code and intellectual property. These companies are particularly attractive to groups like these because they develop widely used enterprise and security products that can be leveraged for future exploits. The primary motive behind these attacks is espionage. Additionally, the capability development involves stealing source code and technical data to exploit unidentified vulnerabilities and weaponize them for future offensive operations. Evidence from recent incidents shows the group exploiting virtualization management systems and appliance software to access internal build systems and code repositories. Some of the techniques most frequently used by this group include cloning domain controllers in order to extract credentials offline and using SOCKS proxies for lateral movement, which suggests a deliberate focus on exploiting the development and management infrastructure for persistent/long-term access. [13]
SaaS Providers / Business Process Outsourcers (BPO)
SaaS providers and BPOs are increasingly targeted because compromising a single provider can expose multiple customer environments. These organizations are targeted because the ability to compromise one provider can give these attackers indirect access to many customer environments. The highlight of their motivation still remains espionage, with a focus on supply chain infiltration rather than direct theft. By utilizing tactics such as phishing, social engineering, or exploiting vulnerabilities in the service provider’s infrastructure, adversaries can embed themselves and quietly collect intelligence from a wide range of downstream organizations without triggering immediate detection. [3] Recent investigations indicate that the campaign’s activity within this sector mirrors other China-linked supply chain operations, which also have the key goal of maintaining stealthy persistence to enable long-term surveillance and selective data exfiltration from compromised environments.
Infrastructure / Appliances & Virtualization Management Systems
Network appliances, VPN gateways, firewalls, and virtualization platforms such as VMware vCenter and ESXi are a key focus for BRICKSTORM. These systems are attractive because they often fall outside the visibility of standard endpoint protection and can be used to maintain deep persistence due to the lack of oversight. The motivation is espionage and operational dominance within these target environments, allowing the attackers to harvest credentials, clone virtual machines for offline analysis, and establish covert tunnels for sustained undetected access. Security analysts have identified BRICKSTORM binaries written in Go, which are tailored to operate within appliance and management systems. The use of SOCKS proxying and DNS-over-HTTPS for encrypted communication enables BRICKSTORM to maintain stealthy and persistent access, aligning with their goals of long-term surveillance and data exfiltration. These campaigns frequently initiate with the exploitation of zero-day vulnerabilities in identified perimeter appliances. To maintain a minimal footprint and evade detection, BRICKSTORM employs sophisticated strategies, including customized malware, secure communication channels, and adaptive evasion techniques, underscoring a calculated approach aimed at achieving long-term infiltration and control. [10,14]
III. Tactics and Techniques
The threat actors behind BRICKSTORM employ sophisticated techniques from initial access to exfiltration in order to complete their mission. The following section outlines the MITRE ATT&CK tactics and techniques observed in use by BRICKSTORM [5,11]:
| TACTIC |
TECHNIQUE |
MITRE ATT&CK ID |
DESCRIPTION |
| Initial Access |
Exploit Public-Facing Application |
T1190 |
Adversaries may exploit vulnerabilities or misconfigurations in internet-facing systems to gain initial network access. |
| Execution |
Command and Scripting Interpreter |
T1059 |
Adversaries may abuse command and script interpreters to execute commands, scripts, or binaries.
|
| Persistence |
Server Software Component: Web Shell |
T1505.003 |
Adversaries may backdoor web servers with web shells to establish persistent access to systems.
|
| Persistence |
Boot or Logon Autostart Execution |
T1547 |
Adversaries may configure systems to automatically execute a program during system boot or logon.
|
| Credential Access |
Credentials from Password Stores |
T1555 |
Adversaries may search for common password storage locations to obtain user credentials.
|
| Credential Access |
OS Credential Dumping |
T1003 |
Adversaries may attempt to dump credentials to obtain account login and credential material.
|
| Lateral Movement |
Remote Services: SSH |
T1021.004 |
Adversaries may use valid accounts to log into remote machines using Secure Shell (SSH) and perform actions.
|
| Defense Evasion |
Obfuscated Files or Information |
T1027 |
Adversaries may attempt to make an executable or file difficult to discover or analyze by encrypting, encoding, or obfuscating its contents.
|
| Command and Control |
Application Layer Protocol: Web Protocols |
T1071.001 |
Adversaries may communicate using application layer protocols associated with web traffic.
|
| Command and Control |
Application Layer Protocol: DNS over HTTPS |
T1071.004 |
Adversaries may communicate using the Domain Name System (DNS) application layer protocol.
|
| Exfiltration |
Exfiltration Over C2 Channel |
T1041 |
Adversaries may steal data by exfiltrating it over an existing command and control channel. |
Table 1. MITRE ATT&CK Techniques Associated with BRICKSTORM
Initial Access
Initial access often begins with the compromise of edge devices and public-facing applications. In at least one of the observed cases, the threat actors have obtained initial access by exploiting unknown, unpatched vulnerabilities, CVE-2024-21893 and CVE-2024-21887, which involve a command injection vulnerability and an authentication bypass in web components of Ivanti Connect Secure and Ivanti Policy Secure. [5, 6, 7]
Execution
Once a foothold is established, BRICKSTORM can accept web-based commands and execute OS commands, returning HTTP responses with the command output. This approach gives threat actors interactive control without the need for interactive shells. BRICKSTORM also blends in with the target environment by matching naming conventions and even functionality in order to masquerade as legitimate activity. Together, these techniques make detection significantly harder. [5]
Persistence
After execution, BRICKSTORM establishes persistence by installing an in-memory Java Servlet filter called BRICKSTEAL, which intercepts and decodes web authentication traffic and harvests credentials. Because BRICKSTEAL is loaded in the RAM and not on disk, it is stealthier and will not show up on simple file scans. Additionally, it modifies startup scripts, such as init.d, rc.local, or systemd, to survive any reboots. [2,5]
Credential Access & Privilege Escalation
BRICKSTORM harvests passwords from secret stores and leverages in-memory credential dumping in order to escalate privileges and gain access to administrator infrastructure. In several of the observed cases, the malware targeted password vaults and configuration repositories within virtual machines and cloud environments to extract service account credentials and API tokens. BRICKSTORM was also observed collecting credentials from both volatile memory and encrypted stores, which provides access to high-privilege accounts. After gaining access to credentials, the group targets domain controllers, virtualization hosts, and backup systems to escalate privileges, then uses those privileges to move laterally and authenticate to additional systems and interfaces. [5]
Lateral Movement
BRICKSTORM moves laterally through the network by using SSH (secure, encrypted remote-shell access) and masking their activity as routine administrative behavior. The threat actors, after compromising valid credentials, connect via SSH from compromised hosts to internal systems to transfer files, deploy tools, and execute commands, while avoiding visible interactive shells. SSH is also remotely enabled through vCenter’s Appliance Management Interface (VAMI), allowing the threat actors to create temporary local accounts, which are then removed to erase any activity traces. [2,5]
Defense Evasion
To evade detection from signature-based and static analysis, BRICKSTORM obfuscates and modifies its variants for each target. The malware is compiled as Go binaries (single-file executables produced by the Go compiler that contain everything it needs to run, even the libraries and run-time) using obfuscation tools that strip out any identifiable strings and symbols to prevent matches with known indicators, and it also executes payloads in memory, deletes installers after use, and masks malicious functions within legitimate processes. Together, these approaches make file-hash or signature-based detection even more challenging. [5]
Command and Control (C2)
BRICKSTORM blends C2 traffic into normal web traffic by using HTTP/HTTPS and encrypted channels to send commands and payloads. The threat actors establish a SOCKS proxy tunnel to move through the compromised system and access any internal services, while hiding C2 activity (via DNS-over-HTTPS) and rapidly rotating short-lived cloud servers (via ephemeral infrastructure), making tracking their servers difficult and traffic appear routine. [9]
Exfiltration
BRICKSTORM threat actors exfiltrate data out of the affected systems by using the same channels used for command and control (C2). The SOCKS proxy tunnel forwards their workstation into the victim network, giving them direct access to pull files from internal shares, code repositories, and endpoints. Additionally, a common theme of these threat actors is to access email accounts and mailboxes of key people in their target organization. [3] They abuse Microsoft Entra ID (formerly Azure Active Directory) applications that are configured with weak permissions, such as mail.read or full_access_as_app, to access the mailboxes of target accounts. [2, 9]
IV. Adversary Tools and Services
BRICKSTORM combines custom-built malware, opensource libraries, and legitimate internet services to maintain long-term access and hide their activity across targeted networks. The following list contains tools and services associated with the BRICKSTORM campaign along with reasoning behind why it is part of the campaign:
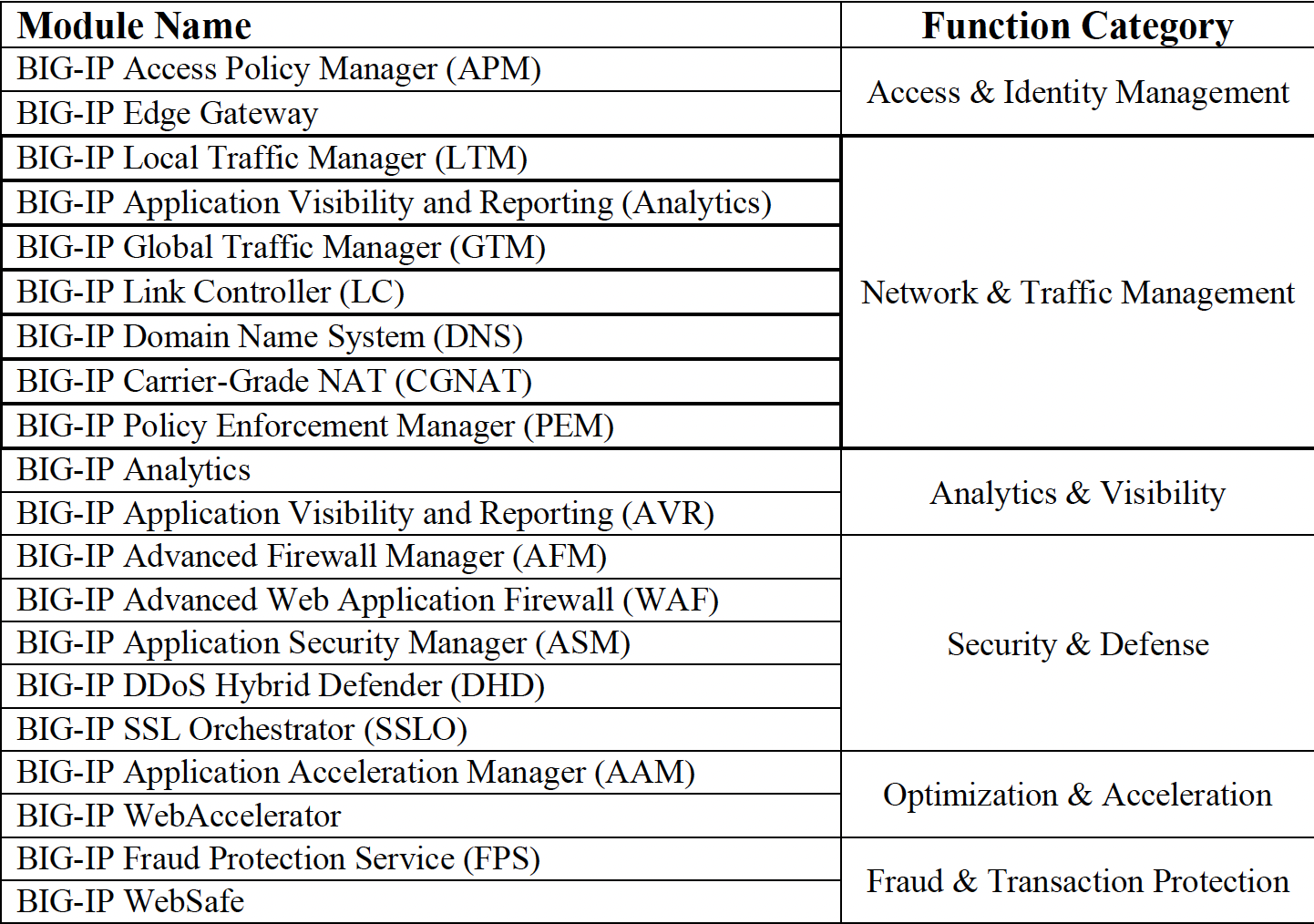
1. Go ELF Backdoor (Pg_update, Listener, Vmprotect)
A Golang-based implant designed to run directly on F5 BIG-IP appliances. [10] It gives attackers remote control, encrypted communications, and data exfiltration without relying on external dependencies (ideal for stable persistence on embedded Linux systems).
2. Yamux (Golang Multiplexing Library)
Allows attackers to send multiple data streams over one TCP or TLS connection, hiding several operations within a single outbound session. [4]
3. SOCKS Proxy Mechanism
Allows pivoting from the compromised appliance management IP to internal hosts, allowing lateral movement while maintaining stealth. [10]
4. TLS / HTTP/2 (ALPN h2) and WebSocket C2 Channels
Encrypted web protocols that blend with legitimate traffic. The connection upgrades to WebSocket for long-term persistence and control.
5. Exploits for 0-days and Known Vulnerabilities
Used to gain initial access to f5’s BIG-IP management interfaces, especially after F5’s source code theft revealed internal vulnerabilities. [1]
6. Public Code Repositories (China-based)
Reuse of legitimate Golang and networking code from public sources, some of which host malicious projects reused for appliance compromise. [10]
7. Cloud/CDN and DNS-over-HTTPS (DoH) Services
Legitimate cloud platforms (like Cloudflare or Heroku) and encrypted DNS channels abused for C2 traffic, domain hiding, and command relay, making detection more difficult. [2]
V. Indicators of Compromise (IOCs)
According to Mandiant’s threat intelligence report called Another BRICKSTORM:Stealthy Backdoor Enabling Espionage into Tech and Legal Sectors, there is diminishing value for using IOCs to detect BRICKSTORM’s presence [3]. TTP-based hunting is a necessary approach to detect patterns that are unlikely to be detected.
The following table presents a Mandiant-adapted checklist for detecting BRICKSTORM activity and associated adversary behaviors:
| Hunt Objective |
Why it matters |
Where to Look for Evidence |
|
1. Create or update an inventory of all appliances and edge devices
|
You can’t hunt what you don’t know exists. Attackers often use private management IPs to send data out of the network.
|
Configuration Management Database (CMDB)
Asset registry
Network Discovery Tools (NMAP, ARP scans)
|
|
2. Scan files and backups for BRICKSTORM malware
|
Attackers often delete malware from live hosts; however, traces may still be preserved in backups
|
Appliance File Systems
Backup Stores and Snapshot Images
|
|
3. Look for internet traffic from appliances
|
Appliances should rarely call unknown Internet hosts. Suspicious outbound traffic may conceal command and control communication
|
Firewall logs
Domain Name System (DNS) logs
Intrusion Detection and Prevention System (IDS/IPS)
NetFlow/Proxy logs
|
|
4. Watch for appliances connecting to Window Systems
|
These devices normally should not log into windows. This could be a sign of lateral movement
|
Endpoint Detection and Response (EDR) telemetry
Windows Security Event Logs
Terminal Services logs
Windows Unified Audit Log (UAL)
|
|
5. Detect access to passwords and credentials
|
Stolen credentials enable privilege escalation or domain compromise.
|
Endpoint Detection and Response (EDR) Forensic Snapshots
Shellbags
Data Protection Application Programming Interface (DPAPI) Artifacts
Browser Profile Access Logs
|
|
6. Monitor 365 mailbox access
|
Actors use mail.read/full_access_as_app to exfiltrate mail at scale, which means they can steal emails and read confidential information.
|
Microsoft 365 Unified Audit Log (UAL)
OfficeActivity Logs
Azure Active Directory (AD) App Registry |
|
7. Check for cloned virtual machines (VMs)
|
Attacker can clone a VM to extract sensitive files offline
|
vSphere VPXD Logs
Virtual Machine (VM) Inventory
Datastore Logs
|
|
8. Watch for new or deleted local admin accounts
|
Short-lived accounts are often created for implant setup or maintaining stealthy access.
|
VMware Audit Events
Single Sign-on (SSO) Logs
Virtual Appliance Management Interface (VAMI) Logs
|
|
9. Monitor SSH enablement on appliances
|
Attackers often enable SSH to manually deploy or manage implants
|
VAMI REST Logs
Configuration Change Logs
|
|
10. Identify unauthorized or suspicious VMs
|
Malicious actors may create fake Virtual Machines to exfiltrate or store stolen data.
|
VM Inventory Reports
Datastore Object Listings
|
Table 2. BRICKSTORM Threat Hunting Reference Table
VI. Recommendations
BRICKSTORM allows attackers to compromise systems and networks while evading detection by common security controls, such as DNS monitoring at the network level. To mitigate these threats, organizations should implement the following defensive strategies:
1. DNS over HTTPS
BRICKSTORM can be configured to operate both with and without DNS over HTTPS (DoH). Therefore, it is recommended that organizations watch for unusual DoH activity to prevent variations of BRICKSTORM that may leverage these services. [8]
2. TLS Inspection
BRICKSTORM can easily blend malicious activity into legitimate HTTPS traffic by using encrypted channels for C2. As a result, organizations should ensure that their TLS inspection detects or blocks nested TLS sessions (encrypted sessions over already encrypted traffic). [8]
3. Behavior-Based Detection
To avoid detection, BRICKSTORM uses the component BRICKSTEAL loaded in the memory, and obfuscates and modifies its variants for each target. Therefore, traditional signature-based detections may fail to detect the backdoor. Organizations should implement EDR solutions capable of performing behavioral anomaly detection to focus on unusual process injections, in-memory Java servlet filters, or unsigned binaries. [3, 5]
4. Principle of Least Privilege
Any device that is internal or internet-facing should be configured to follow the principle of least privilege. Devices should be outbound only to vendor update servers, package repositories, or support endpoints. Therefore, firewalls should be in place to monitor and allow access only to authorized domains and IPs necessary for devices to operate. [3]
5. Patch and Harden Systems
Vendor updates should be applied to all systems, and outbound connectivity should be restricted for management interfaces. [2]
6. Threat Hunting & Detection Logic
Based on the identified TTPs and Indicators of Compromise, organizations are encouraged to perform threat hunts and put in place detection rules to proactively detect BRICKSTORM. [2]
7. Access Controls
SSH is remotely enabled through vCenter’s Appliance Management Interface (VAMI) to allow threat actors to create temporary local accounts. Therefore, MFA should be enforced for vCenter’s Appliance Management Interface (VAMI), while also monitoring VM cloning. Additionally, BRICKSTORM abuses Microsoft Entra ID applications and its permissions, making it fundamental for organizations to review permissions such as mail.read or full_access_as_app. [2,3]
By following these recommendations and defensive strategies, organizations can proactively defend themselves from BRICKSTORM.
VII. References
[1] Cybersecurity and Infrastructure Security Agency. (2025, April). Emergency Directive 26-01: Mitigate vulnerabilities in F5 devices. https://www.cisa.gov/news-events/directives/ed-26-01-mitigate-vulnerabilities-f5-devices
[2] Fortinet. (2025, April 10). BRICKSTORM espionage campaign: Threat Signal Report 6204. FortiGuard Threat Intelligence. https://www.fortiguard.com/threat-signal-report/6204/brickstorm-espionage-campaign
[3] Google Threat Intelligence Group. (2025, September 24). Another BRICKSTORM: Stealthy backdoor enabling espionage into tech and legal sectors. Google Cloud Threat Intelligence Blog. https://cloud.google.com/blog/topics/threat-intelligence/brickstorm-espionage-campaign
[4] HashiCorp. (n.d.). Yamux: Golang multiplexing library. GitHub repository. https://github.com/hashicorp/yamux
[5] Mandiant (Intelligence Team). (2025, March). BRICKSTORM malware: UNC5221 targets tech and legal sectors in the United States. Picus Security Blog. https://www.picussecurity.com/resource/blog/brickstorm-malware-unc5221-targets-tech-and-legal-sectors-in-the-united-states
[6] National Institute of Standards and Technology. (2023). CVE-2023-46805: Authentication bypass in Ivanti Connect Secure. National Vulnerability Database. https://nvd.nist.gov/vuln/detail/CVE-2023-46805
[7] National Institute of Standards and Technology. (2024). CVE-2024-21887: Command injection vulnerability in Ivanti Connect Secure and Policy Secure. National Vulnerability Database. https://nvd.nist.gov/vuln/detail/CVE-2024-21887
[8] NVISO Labs. (2025, April). BRICKSTORM malware analysis report. NVISO Threat Intelligence Blog. https://blog.nviso.eu/wp-content/uploads/2025/04/NVISO-BRICKSTORM-Report.pdf
[10] ReSecurity. (2025, April 15). F5 BIG-IP source code leak tied to state-linked campaigns using BRICKSTORM backdoor. ReSecurity Threat Intelligence Blog. https://www.resecurity.com/blog/article/f5-big-ip-source-code-leak-tied-to-state-linked-campaigns-using-brickstorm-backdoor
[11] The MITRE Corporation. (2025). MITRE ATT&CK framework: Techniques and tactics. https://attack.mitre.org/ 14 of 14
[12] Bloomberg. (2025, September 24). ’Most prevalent’ Chinese hacking group targets tech, law firms. Bloomberg News. https://www.bloomberg.com/news/articles/2025-09-24/-most-prevelant-chinese-hacking-group-targets-tech-law-firms
[13] Burt, J. (2025, September 24). Chinese hackers steal data from U.S. legal, tech firms for more than a year. Security Boulevard. https://securityboulevard.com/2025/09/chinese-hackers-steal-data-from-u-s-legal-tech-firms-for-more-than-a-year/
[14] Lakshmanan, R. (2025, September 24). UNC5221 uses BRICKSTORM backdoor to infiltrate U.S. legal and technology sectors. The Hacker News. https://thehackernews.com/2025/09/unc5221-uses-brickstorm-backdoor-to.html
[15] Arctic Wolf Networks. (2025, October 30). UNC6384 weaponizes ZDI-CAN-25373 vulnerability to deploy PlugX against Hungarian and Belgian diplomatic entities. Arctic Wolf. https://arcticwolf.com/resources/blog/unc6384-weaponizes-zdi-can-25373-vulnerability-to-deploy-plugx/
[14] Google Threat Intelligence Group. (2025, August 25). PRC-Nexus espionage campaign hijacks web traffic to target diplomats. Google Cloud Blog. https://cloud.google.com/blog/topics/threat-intelligence/prc-nexus-espionage-targets-diplomats
[15] Mandiant. (2025, September 24). Another BRICKSTORM: Stealthy Backdoor Enabling Espionage into Tech and Legal Sectors. Google Cloud Blog. https://cloud.google.com/blog/topics/threat-intelligence/brickstorm-espionage-campaign
[16] The Hacker News. (n.d.). UNC5221 uses BRICKSTORM backdoor to infiltrate U.S. legal and technology sectors. https://thehackernews.com/2025/09/unc5221-uses-brickstorm-backdoor-to.html
Threat Advisory created by The Cyber Florida Security Operations Center. Contributing Security Analysts: Waratchaya Luangphairin (June), Eduarda Koop, and Isaiah Johnson