
I. Targeted Entities
- NetScaler Users*
II. Introduction
This cyberattack has been targeting NetScaler application delivery controller (ADC) and NetScaler Gateway; tools that improve the delivery speed of applications to an end user and provides secure remote access to application and services, respectively. Threat actors exploited this vulnerabiltiy as a zero-day attack to drop a webshell. The webshell allowed the threat actors access to the victim’s active directory (AD) and collect and exfiltrate data.
III. Additional Background Information
In June 2023, threat actors exploited a public facing applications called NetScaler Application Delivery Controller and NeScaler Gateway. Threat actors implanted a webshell on the organization’s NetScaler ADC appliance, and then abused elevation controls to initilalize an exploit chain to a binary file to extract data.
The affected versions following this vulnerability are for Netscaler and Netscaler Gateway: 13.1 before 13.1-40.13. Intially, CVE-2023-3519 was CVE-2019-19781 that as discovered in December 2019 and it attracted signifcant attention due to its potential to be exploited for the same purpose as it is being seen (unauthneticated remote code execution). In the 2019-29781 CVE attackers would gain access through Citrix NetScaler server to exploit public facing applications such as Citrix ADC and gateway and we can see that happening in the 2023-3519 CVE as well.
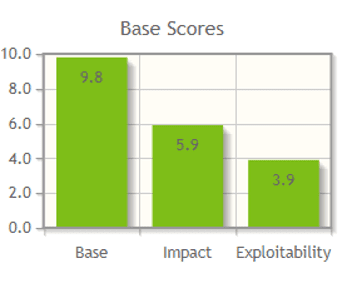
According to NISTs’ CVSS Severity and Metrics the vulnerability has been rate the following:
Threat Actor Activity
Victim 1
As part of their initial exploit chain [T1190], the threat actors uploaded a TGZ file [T1105] containing a generic webshell [T1505.003], discovery script [TA0007], and setuid binary [T1548.001] on the ADC appliance and conducted SMB scanning on the subnet [T1046].
Threat Actor Activity
Victim 2
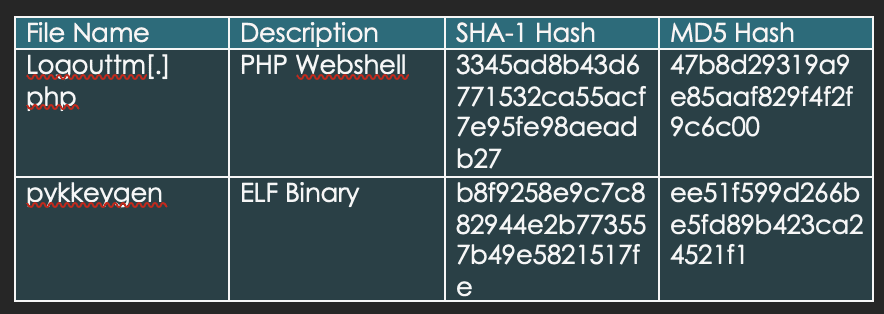
Threat actors uploaded a PHP webshell *logouttm.php* [T1036.005], likely as part of their initial exploit chain, to */netscaler/ns_gui/vpn/. Within an hour of installing the webshell, the actors implanted an Executable and Linkable Format (ELF) binary pykeygen that set user unique identifier (UID) to root and executed /bin/sh [T1059.004] via setuid and execve syscall.* [T1106]. Note: A third party also observed threat actors use an ELF binary (named pip4) to execute /bin/sh via syscall and change the UID to root. pip4 was located at /var/python/bin.
With root level access, the actors used hands-on-keyboard for discovery. They queried the AD via ldapsearch for users, groups, and computers. They collected the data in gzipped text files renamed 1.css and 2.css and placed the files in /netscaler/ns_gui/vpn/ for exfiltration.
After exfiltrating the files, the actors deleted them from the system [T1070.004] as well as some access logs, error logs, and authentication logs [T1070.002]. The victim organization detected the intrusion and mitigated the activity but did not identify signs of additional malicious activity.
For command and control (C2), the actors appeared to use compromised pfSense devices [T1584]; the victim observed communications with two pfSense IP addresses indicating the actor was using them for multi-hop proxying C2 traffic [T1090.003].
Updated vulnerabilities affecting Netscaler ADC and Netscaler Gateway:
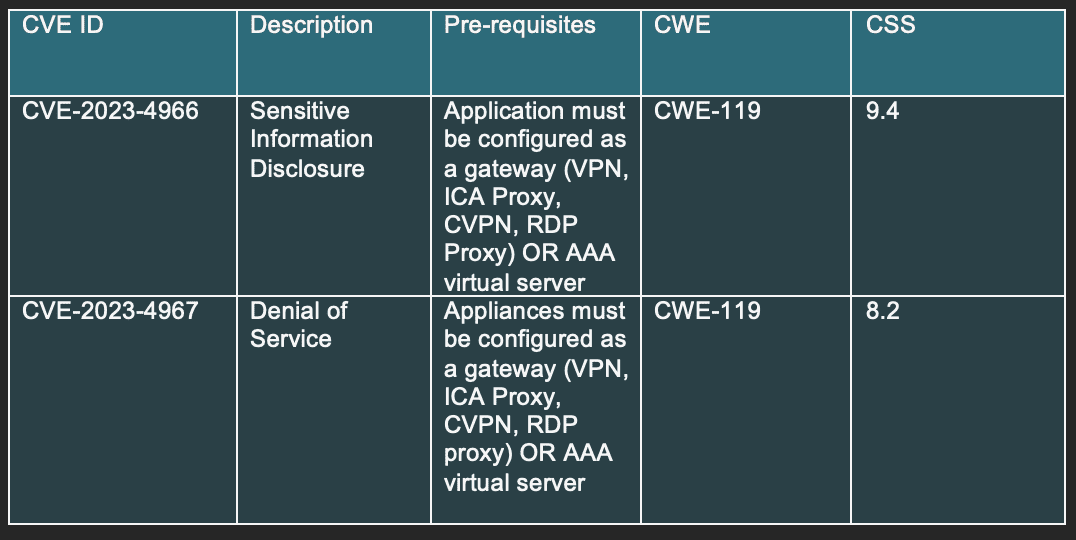
As of October 23rd, Cyber Florida recived updates regarding vulnerabilities affecting Netscaler ADC and Netscaler Gateway. The vulnerabilities in mention: CVE-2023-4966 and CVE 2023-4967 both place high in the CVSS score for severity, and should be mitigated immediately. CVE-2023-4966, a sensitive information disclosure vulnerability, allows attackers to get access to large amounts of data in memory at the end of a buffer. Frequently seen within this attack vector are efforts to gain unauthetnicated access to previous session tokens that allow attackers impersonate authenticated users and their escalate priveleges. CVE 2023-4967, although less critical than the first observed vulnerability, is still a severe vulnerability that can lead to a Denial of Service (D.O.S) attack and cause great harm to a company.
As of October 23rd, updated effected versions of Netscaler ADC and Netscaler Gateway are the following:
- Netscaler ADC and Netscaler Gateway 14.1 before 14.1-8.50
- Netscaler ADC and Netscaler Gateway 13.1 before 13.1-49.15
- Netscaler ADC and Netscaler Gateway 13.0 before 13.0-92.19
V. MITRE ATT&CK
- T1190 – Exploit Public-Facing Applications
Adversaries may attempt to exploit a weakness in an Internet-facing host or system to initially access a network. The weakness in the system can be a software bug, a temporary glitch, or a misconfiguration. Adversaries exploited CVE-2023-3519 to implant a webshell on the organization’s NetScaler ADC appliance.
- T1505.003 – Server Software Component: Web Shell
Adversaries may backdoor web servers with web shells to establish persistent access to systems. The threat actors implanted a generic webshell on the organization’s NetScaler ADC appliance.
- T1548.001 – Abuse Elevation Control Mechanism: Setuid and Setgid
An adversary may abuse configurations where an application has the setuid or setgid bits set in order to get code running in a different (and possibly more privileged) user’s context. As part of their initial exploit chain, the threat actors uploaded a TGZ file contain a setuid binary on the ADC appliance
- T1036.008 – Masquerading: Masquerade File Type
Adversaries may masquerade malicious payloads as legitimate files through changes to the payload’s formatting, including the file’s signature, extension, and contents. Various file types have a typical standard format, including how they are encoded and organized. The threat actors exfiltrated data by uploading it as an image file to a web-accessible path.
- T1018 – Remote System Discovery
Adversaries may attempt to get a listing of other systems by IP address, hostname, or other logical identifier on a network that may be used for Lateral Movement from the current system. Functionality could exist within remote access tools to enable this, but utilities available on the operating system could also be used such as Ping or net view using Net.The threat actors queried the AD for computers. The threat actors attempted to execute a subnet-wide curl command to identify what was accessible from within the network as well as potential lateral movement targets. Network-segmentation controls prevented this activity.
- T1016.001 – System Network Configuration Discovery: Internet Connection Discovery
Adversaries may check for Internet connectivity on compromised systems. This may be performed during automated discovery and can be accomplished in numerous ways such as using Ping, tracert, and GET requests to websites.The threat actors attempted to verify outbound network connectivity with a ping command and executed host commands for a subnet-wide DNS lookup. Networksegmentation controls prevented this activity.
- T1046 – Network Service Discovery
Adversaries may attempt to get a listing of services running on remote hosts and local network infrastructure devices, including those that may be vulnerable to remote software exploitation. Common methods to acquire this information include port and/or vulnerability scans using tools that are brought onto a system. The threat actors conducted SMB scanning on the organization’s subnet.
- T1056.001 – Archive Collected Data: Archive via Utility
Adversaries may use utilities to compress and/or encrypt collected data prior to exfiltration. Many utilities include functionalities to compress, encrypt, or otherwise package data into a format that is easier/more secure to transport.The threat actors encrypted discovery data collected via openssl in “tar ball.”
- T1090.001 – Proxy: Internal Proxy
Adversaries may use an internal proxy to direct command and control traffic between two or more systems in a compromised environment. Adversaries use internal proxies to manage command and control communications inside a compromised environment, to reduce the number of simultaneous outbound network connections, to provide resiliency in the face of connection loss, or to ride over existing trusted communications paths between infected systems to avoid suspicion.The actors likely used a PHP shell with proxying capability to attempt proxying SMB traffic to the DC (the traffic was blocked by a firewall and account restrictions).
- T1531 – Account Access Removal
Adversaries may interrupt availability of system and network resources by inhibiting access to accounts utilized by legitimate users. Accounts may be deleted, locked, or manipulated (ex: changed credentials) to remove access to accounts. The threat actors deleted the authorization configuration file (/etc/auth.conf)—likely to prevent configured users from logging in remotely (e.g., CLI).
VI. Recommendations
- Install the relevant updated versions as soon as possible.
- Check for files newer than the last installation.
- Quarantine or take offline potentially affected hosts.
- Provision new account credentials.
- Collect and review artifacts such as running processes/services, unusual authentications, and recent network connections.
- Apply robust network-segmentation controls on NetScaler appliances, and other internet-facing devices.
- Test and validate security controls to determine their performance against threat behaviors associeted with the MITRE ATT&CK in this advisory.
VII. IOCs (Indicators of Compromise)
IOC’s Affiliated with Citrix CVE-2023-3519 Exploitation
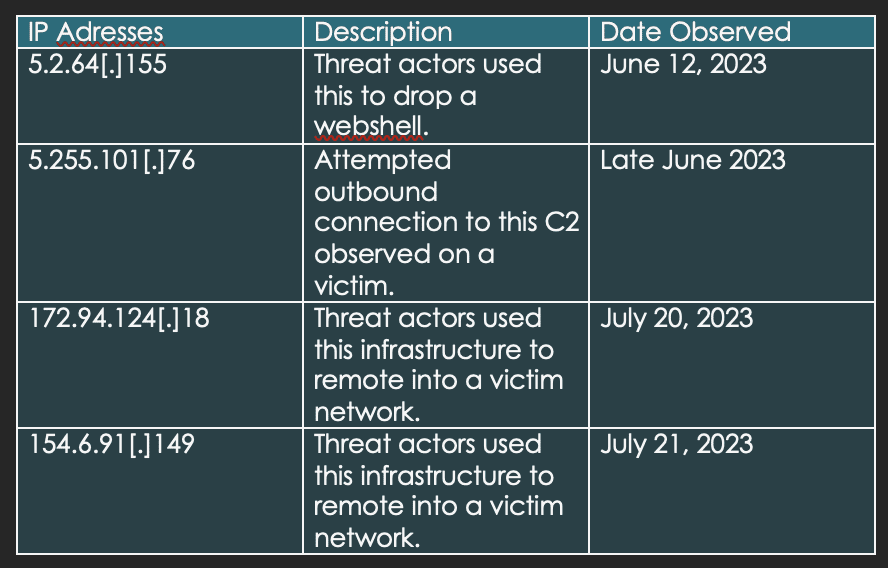
Third-party provide IP addresses afiliated with Citrix CVE-2023-3519
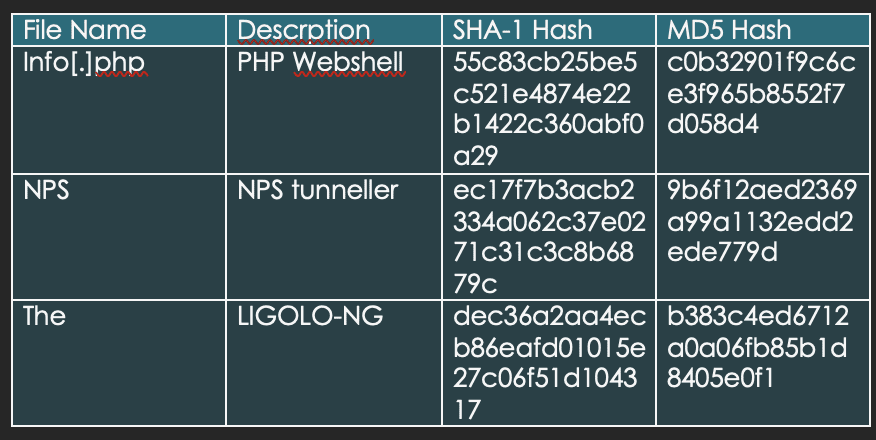
Third-party provided IOCs affiliated with Citrix CVE-2023-3519
Updated NetScaler ADC and NetScaler Gateway containing unathenticated buffer-related vulnerablities *10/23/2023*
VIII. References
Threat actors exploiting Citrix CVE-2023-3519 to Implant Webshells – CISA. https://www.cisa.gov/sites/default/files/2023-07/aa23-201a_csa_threat_actors_exploiting_citrix-cve-2023-3519_to_implant_webshells.pdf
Enterprise Techniques. Mitre ATT&CK®. (n.d.). https://attack.mitre.org/versions/v13/techniques
NetScaler ADC and NetScaler Gateway Security Bulletin for CVE-2023-4966 and CVE-2023-4967. (2023, October 23). https://support.citrix.com/article/CTX579459/netscaler-adc-and-netscaler-gateway-security-bulletin-for-cve20234966-and-cve20234967
Rapid. (n.d.). CVE-2023-4966: Exploitation of Citrix NetScaler Information Disclosure Vulnerability. Rapid7. https://www.rapid7.com/blog/post/2023/10/25/etr-cve-2023-4966-exploitation-of-citrix-netscaler-information-disclosure-vulnerability/#:~:text=On%20October%2010%2C%202023%2C%20Citrix,the%20end%20of%20a%20buffer.
Threat Advisory created by The Cyber Florida Security Operations Center. Contributing Security Analysts: EJ Bulut, Nahyan Jamil, Alessandro Lovadina, Ben Price, Erika Delvalle, Ariana Manrique, Yousef Blassy
