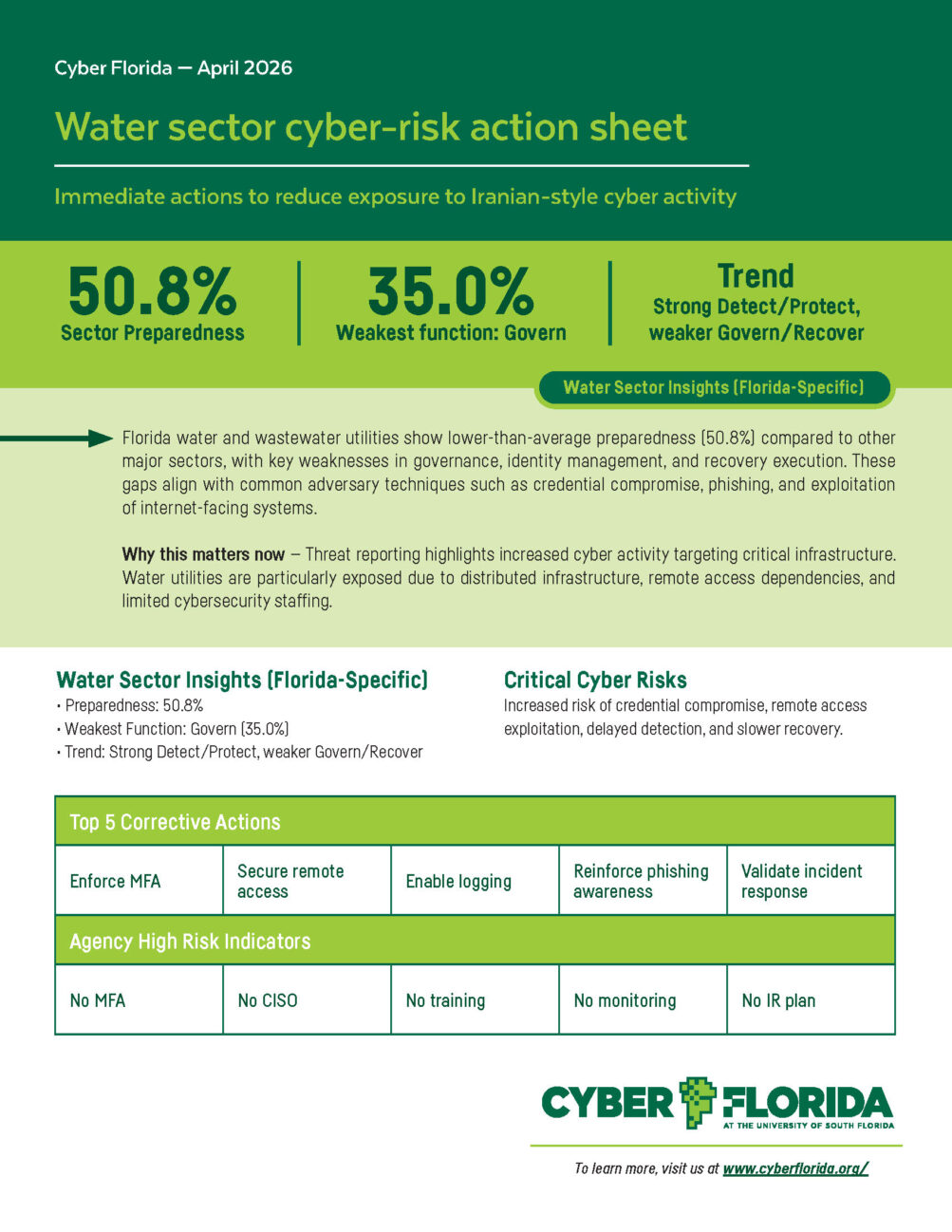
Water Sector Cyber-Risk Action Sheet
Through a search of publicly available news sources, we identified 30 ransomware incidents in the state of Florida occurring between 2020 and 2024. This is an increase from 18 ransomware incidents between 2016 and 2019 (see Florida Ransomware Incidents 16-19). Ransomware attacks have been on the rise against these targets: government agencies, local emergency services, hospitals, small and medium-sized businesses, and small NGOs. The attacked targets share a number of common features: (1) most targeted entities relied heavily on centralized information technology (IT) and operational technology (OT) infrastructures; (2) they were generally not large, high-profile service providers; (3) they did not extensively investigate the incident or seek to attribute or take official action to report or prosecute those responsible; and (4) they typically had sufficient financial resources to pay out a ransom demand. Read our in-depth report for more insights.

Join the Army Cyber Institute, Cyber Florida, and partners for an immersive, multi-sector cyber exercise that follows a coordinated cyberattack on the Tampa water sector.
Dates: May 18 – 20
Location: USF Marshall Student Center, Tampa, FL
Cost: FREE
United States military installations and their surrounding communities share an interest in the resiliency of cyber-critical infrastructure systems. In addition to civil-military interdependencies, a failure in one critical infrastructure sector can cause cascading effects across others. The Army Cyber Institute (ACI) launched the Jack Voltaic® (JV) initiative to address gaps and build resilience.
Utility operators, IT/OT security personnel, emergency managers, city/county leaders, and military base personnel.
Realistic Scenario: A high-stakes, simulated cyberattack affecting local businesses, public sector infrastructure, and nearby military bases.
Build Relationships: Enhance collaboration between public, private, and military entities to build regional resilience.
Parallel Training Platforms
Cyber threats are evolving rapidly. In 2024 alone, the U.S. reported over $50.5 billion in losses and 4.2 million cybercrime complaints. Florida ranked third nationwide – behind only California (1st) and Texas (2nd) – in both complaints and financial losses (FBI, 2024). These threats impact not only the government but also businesses, nonprofits, families, and individuals across communities.
Today’s risks include social engineering, phishing/spoofing, ransomware, extortion, data breaches, and increasingly Artificial Intelligence (AI) attacks, such as deepfakes and automated intrusions. These tactics threaten not just infrastructure, but also public trust and operational continuity. Yet many local, state, and federal employees still lack
access to effective cybersecurity education and awareness training. Existing initiatives often measure success through certificates, digital badges, or job placement, but rarely assess real-world performance, behavior change, or mission readiness. As a result, public-sector agencies remain vulnerable.
This report identifies key challenges in cybersecurity education and awareness programs for state and local government employees and presents strategies to help build cyber-literate and resilient communities across Florida – at work, in public service, and beyond.
For small and medium businesses working on federal contracts, the new Cybersecurity Maturity Model Certification (CMMC) can seem overwhelming. Cyber Florida’s new CMMC L1 Guide helps put the new standards into simple language and actionable steps.

Cyber Florida’s Critical Infrastructure Program (CIP) Workshop brings together public-sector leaders, IT professionals, and emergency managers to tackle real-world cyber threats facing Florida’s essential services. These hands-on sessions deliver practical tools, expert insights, and interactive scenarios designed to help SLTT agencies strengthen their cyber resilience and readiness.
Whether you’re securing water systems, transportation networks, or municipal services, these workshops are your front line in building a safer Florida. Don’t miss this chance to improve your cybersecurity posture and resilience!
The coordinated “typhoon” campaigns, led by actors like Volt Typhoon, reflect a new phase of state-sponsored cyber warfare that demands a comprehensive U.S. and allied response integrating cybersecurity, intelligence, diplomacy, and legal reform. Dive into the McCrary Institute’s comprehensive brief on this persistent threat.
