Florida’s Largest High School Cyber Competition Breaks Records, Inspires Futures
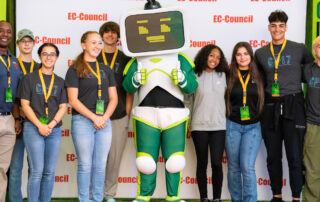
Nearly 1,000 high school students, teachers, and chaperones from across the state descended on the Caribe Royale Resort in Orlando on April 4 for Cyber Florida’s annual CyberLaunch, the nation’s largest in-person, state-sponsored high school cybersecurity competition. And the excitement on the competition floor? Unmatched!
Hosted by Cyber Florida, CyberLaunch 2025 brought together students from 99 schools across 49 districts, including Florida’s five largest school districts and its smallest—LaFayette. In just its second year, CyberLaunch has grown into a premier showcase of talent and opportunity, offering a platform for students to shine and discover future careers in cybersecurity.
I would like to take this opportunity and thank all of Cyber Florida for putting this together.
It really is a wonderful opportunity and platform for the cybersecurity students of Florida to shine.
— Maria Halley Hernandez, John A. Ferguson Senior High School
The Ultimate Cyber Kickstart
Designed to familiarize high school students with the exciting world of cybersecurity, CyberLaunch featured a hands-on capture-the-flag (CTF) style challenge, inspiring keynotes, breakout sessions for educators, and opportunities for students to interact with industry professionals to gain insights into cybersecurity careers.
This year’s event also welcomed 18 career and technical education administrators from 12 school districts, highlighting growing support from school systems eager to expand cybersecurity learning in classrooms.
CyberLaunch 2025 wasn’t just about what happened in one day—it was the culmination of weeks of preparation. Participating teachers and students received access to a library of practice materials and classroom-ready activities that helped demystify cybersecurity concepts and build skills leading up to the big day.
Thank you for an amazing event. My students smiled the entire way home.
We plan on starting an IT Club next Sept.
– Capt. Tim McAllister, Orange Park High School
A Mission in Motion
CyberLaunch is more than a one-day event—it’s a key part of Cyber Florida’s mission to cultivate a robust cybersecurity workforce and create opportunities for every Florida student. Thanks to support from the Florida Legislature and private donors, Cyber Florida ensured that access to this event was obtainable by making the event free to all students and schools.
And the outcomes speak for themselves: students walked away energized, curious, and, in many cases, ready to learn more about the field, and start IT/cybersecurity clubs if they didn’t have one in place already. Teachers gained tools to help bring cybersecurity into their classrooms. And Florida took another big step forward in building digital resilience from the ground up.
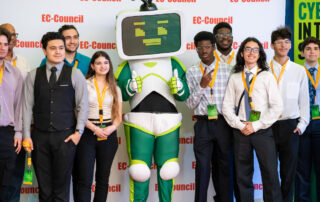
And the Winners Are…
After an intense day of solving puzzles, cracking codes, and working as a team under pressure, a few schools rose to the top. We’re proud to announce the winning teams of CyberLaunch 2025:
Advanced level
1st Place: John A. Ferguson Sr High, Miami-Dade
Teacher: Maria Halley Hernandez
Students: Michael Lopez, Sabrina Chile, Rachel Diaz
2nd Place: 2: East River/Boone High Schools, Orange
Teacher: James Mitchell
Students: Zane Strait (Boone), Brady Graham (Boone), Jamal Santiago (Boone), Bi Trinh (East River)
3rd Place: John A. Ferguson Sr High, Miami-Dade
Teacher: Maria Halley Hernandez
Students: Fabio Martin, Gabriel Barreto Otero, Dominic Hung, Angelo Isasi
Intermediate level
1st Place: Hialeah Gardens, Miami-Dade
Teacher: Rein De Armas
Students: Daniel D. Alvarez, Jean M. Hernandez, Luis E. Lovera
2nd Place: Crooms Academy of Information Technology, Seminole
Teacher: Halima Fisher
Students: Mikhail Tyukin, Anish Miryala, Alyssa Durand, Zane DeReamer
3rd Place: Suncoast Polytechnical High School, Sarasota
Teacher: Stephen McCormack, Lucinda Schlotterback
Students: Lucas Mattos, Maria Kadochnikova, Ben Kuzmik, Szymon Stead-Topor
Beginner level
1st Place: Angeline Academy of Innovation, Pasco
Teacher: Michael Marchesano
Students: Chris Workentin, Logan Prescott, Malakai Jefferson, Christopher Devoe
2nd Place: Timber Creek High School, Orange
Teacher: Daniel Foster
Students: Eoghan Riley, Tomas Lopez Devia, Matthew Nguyen
3rd Place: iPrep Academy North, Miami-Dade
Teacher: Yoel Monzote
Students: Raiya Cohen, Brianna Louissaint, Ariadna Monzon
These standout students demonstrated critical thinking, collaboration, and technical excellence under pressure—and we can’t wait to see where their cyber journeys take them next.
We are so grateful for all the time, energy, and care you put into making this event such a meaningful experience for the students.
It was truly impressive, and very much appreciated.
– Christine Ackerman, Middleburg High School
Looking Ahead
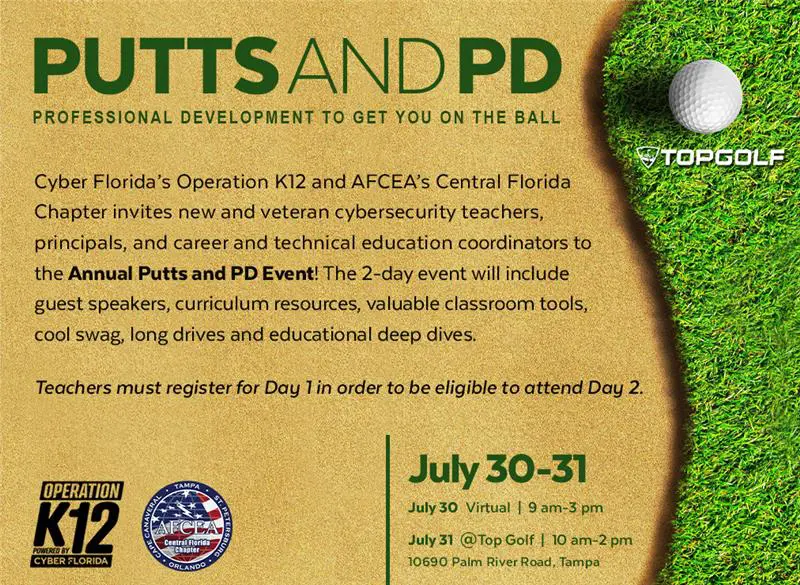
CyberLaunch will return with even more opportunities, more resources, and more students ready to make their mark. Whether you’re a teacher looking to bring cybersecurity into your classroom or a student curious about coding, hacking, and solving digital problems, Cyber Florida’s Operation K12 is your starting point.
To stay informed about next year’s competition, resources, and updates, follow Cyber Florida on social media and visit cyberflorida.org.
A HUGE thank you to our generous and amazing sponsors for supporting this important event!
Universe Sponsor
USF Youth Experience
Orbit Sponsors
AFCEA Central Florida chapter
Bluum
Certification Partners
CompTIA
HP
Prodigy Learning
Teaching Digital Natives
Liftoff Sponsors
EC-Council
Knowledge Pillars
Launchpad Sponsors
Certiport
Dark Enterprise Inc
Guardian Cyber
Marcraft
Siemens
UTeach UTexas
Starbase Supporters
Crespo AI
EDVision
Jamal Rodman
USF World
Zscaler Inc