FirstLine – registration request received
Thank you! We received your request to attend one of our upcoming exercises/courses. The FirstLine team is reviewing your information and will contact you shortly.
Thank you! We received your request to attend one of our upcoming exercises/courses. The FirstLine team is reviewing your information and will contact you shortly.
This webinar will cover how to plan a simple roadmap and additional recommendations for getting started defending your company from Cybersecurity attacks.
For FloridaMakes clients working with Defense customers, provided is an overview of the Department of Defense Cybersecurity Maturity Model Certification (CMMC) program, and recommendations for getting started and achieving this critical compliance requirement.
Speakers will present the no-cost programs and services available to Florida companies, including the Critical Infrastructure Risk Assessment.
The presentation will conclude with next steps and additional resources to get you on a path toward CMMC compliance.
Finally, extra time will be allocated for a robust Q&A starting with a review of the concerns posed at the prior webinar.
Key Takeaways:

Teacher: Jim Brockman
School: Plant High School
County: Hillsborough
Meet Jim Brockman, a fantastic teacher at Plant High School in Hillsborough County. Originally from Cincinnati, Ohio, Jim has been a passionate educator since the start of his career. After teaching in Ohio and Kentucky, he moved to Tampa, Florida, in 2005 to join Jefferson High School, where his dedication to teaching and student success quickly stood out.
In 2010, he joined Strawberry Crest High School to lead the IB Physics program, playing a key role in shaping the school’s academic environment. Now in his fourth year at Plant High, Jim has expanded his expertise to include computer science and cybersecurity, pioneering the integration of advanced technology into the curriculum.
His contributions to curriculum development in Hillsborough County Public Schools are significant—he has written state course descriptions and exam content. Beyond academics, Jim has coached various extracurricular teams and founded Tampa’s first high school rowing club.
Embracing the opportunity to teach cybersecurity, Jim sees it as a modern solution to the decline of vocational programs, offering students both immediate job prospects and pathways to further education.
Outside the classroom, Jim is also an accomplished musician and a founding member of the band Dads of Lore, showcasing his diverse talents and dedication to enriching lives.
Jim Brockman’s career exemplifies his commitment to education and innovative teaching. He has made a lasting impact on students and the broader educational community.
Would you like to be featured in our Teacher Spotlight? To nominate yourself or another deserving teacher, complete the interest form below!
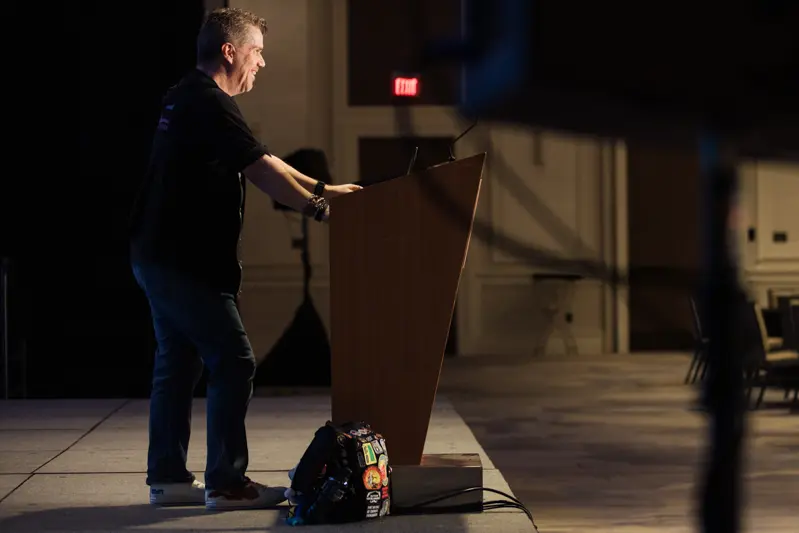
On this episode, we sit down with Rob Allen, the Chief Marketing Officer at ThreatLocker, live from the 2024 Sunshine Cyber Conference. From his early days “locked” in an IT closet to his current role in the C-suite, Rob’s journey is one of curiosity, adaptation, and a passion for cybersecurity. At ThreatLocker, he takes customer ideas and use cases and transforms them into solutions for organizations of all sizes.
Rob shares why businesses shouldn’t fear the “deny by default” approach, explaining how the zero-trust mindset is essential in today’s threat landscape. He also discusses with hosts Jack Clabby of Carlton Fields, P.A., and Kayley Melton, Director for Strategic Initiatives at the Cognitive Security Institute and the Bob Ross of infosec, how media coverage often distorts public perception of cybersecurity by only highlighting major breaches and incidents.
In the Lifestyle Polygraph segment, Rob reveals his love for Apple products, why he wishes he could have met Steve Jobs, and his obsession with Buc-ee’s brisket sandwiches. He also shares a hilarious (and perhaps exaggerated) story about the Cyber Florida team “infiltrating” ThreatLocker and taking his backpack back to Tampa!
You can learn more about ThreatLocker, here: https://www.threatlocker.com
You can follow Rob Allen on LinkedIn here: https://www.linkedin.com/in/threatlockerrob/
This 16-hour course provides guidance on building and executing a robust cybersecurity incident recovery program, covering both pre- and post-incident stages. It bridges IT and emergency management to help government, critical infrastructure, and private-sector personnel effectively respond to and recover from cyber disruptions.
Through interactive discussion and practical exercises, participants will learn best practices and tactical strategies for restoring operations following a cyber-attack. By the end of this course, you’ll be equipped to strengthen organizational resilience, manage cyber incidents more effectively, and build an action plan for continued readiness.
As part of a Department of Homeland Security/Federal Emergency Management Agency (DHS/FEMA) cooperative agreement training program, this course is available at no direct cost to state, county, and local government agencies.
Key Topics Include:
Suggested Audience
Upon successful completion, you will be able to:
Enrollment Requirements
Participants must be U.S. citizens. A FEMA Student ID is required to register for and participate in any training provided by FEMA agencies. All FEMA training providers, registration systems, and enrollment procedures are required to use this FEMA SID, which can be obtained at the following website: https://cdp.dhs.gov/femasidopens in a new tab; or with TEEX assistance upon arrival for class.

Participants will engage in an exciting tabletop exercise hosted by the NUARI, offering hands-on experience in responding to cyber incidents. A free lunch will be provided, along with opportunities to network with cybersecurity experts and industry peers.
Don’t miss this chance to improve your cybersecurity posture and resilience!

This webinar will underscore the crucial role of basic research in driving cybersecurity innovation from a multidisciplinary perspective and raise awareness within the academic community about UC2’s interest in partnering to fund groundbreaking basic research in cybersecurity.
With a welcome introduction by National Defense University’s President, VADM Peter A. Garvin, USN, guest speakers from Space Force, Air Force and Minerva Research Initiative will address cyber strategy for Space Force, levels of basic research and technological applications, research requirements, future-focused discussions, and human-centered needs.
Speakers:
Register today to join this conversation about the transformative potential of basic research in cybersecurity and discover exciting opportunities for academic partnerships with UC2.
Communication, Collaboration and Access: UC2 aims to fill this gap through its mission of increasing communication, collaboration, and access. UC2 funds basic and applied research. With a strong focus on partnerships, UC2 measures the impact of collaboration. UC2 believes that partnership will influence how research is transferred into the hands of users and also the DoD challenges are transferred back to the academic teams who can address them.






















































































2026 Dates:
12 & 13 March 2026
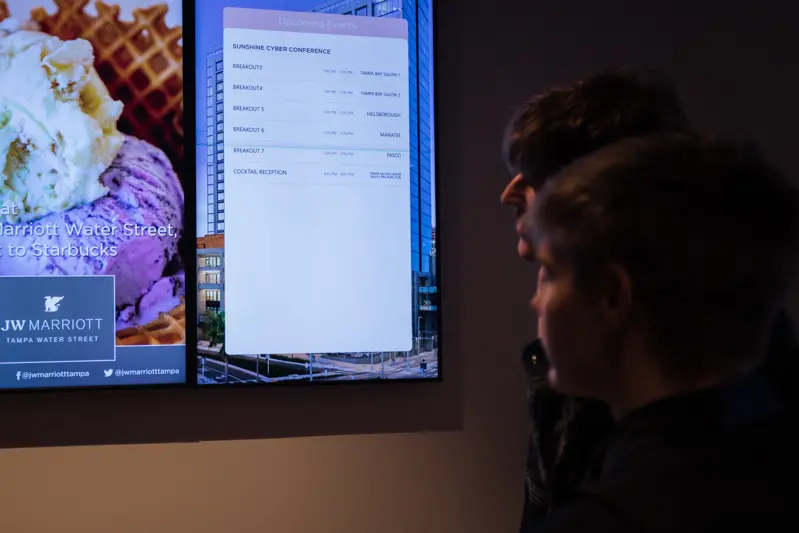
Sunshine Cyber Conference 2025 was an electrifying gathering of cybersecurity professionals, students, and industry leaders. With more than 500 attendees, the event was packed with energy, innovation, and invaluable insights. From cutting-edge keynote sessions to hands-on workshops, attendees had the opportunity to engage with some of the brightest minds in cybersecurity.
One of this year’s conference highlights was the 29 meet-ups scheduled through the Whova app, allowing participants to connect, collaborate, and exchange ideas seamlessly. The outstanding speakers and thought-provoking sessions left a lasting impact, covering topics ranging from emerging cyber threats to best practices in digital defense.
This event wouldn’t have been possible without the generous support of our sponsors. We extend our heartfelt gratitude to:
Your contributions helped make this event a phenomenal success!
We were thrilled to host an incredible lineup of exhibitors, each bringing unique expertise and innovations to the table:
Sunshine Cyber Conference 2025 was a testament to the power of collaboration in the cybersecurity space. We can’t wait to see what the future holds for this growing community. Thank you to everyone who attended, spoke, and contributed to making this event truly exceptional.
Stay tuned for details on Sunshine Cyber Conference 2026—we’ll be back bigger and better than ever!
