Putts & PD 2025

In this webinar, the University of Florida’s Dr. Nancy Ruzycki and Cyber Florida’s Operation K12 will explore how cyber teachers can bring in AI frameworks and tools in the cyber classroom.
This session will look at generative AI and deepfakes, and the role of cyber professionals in protecting consumers from misinformation.
Early this morning, a widespread fault with Microsoft Windows machines running the CrowdStrike Falcon agent caused chaos around the globe – grounding flights, taking banks, hospital systems, and media offline, and causing a massive global disruption to companies and services around the world.
Cybersecurity firm CrowdStrike said that the issue believed to be behind the outage was not a security incident or cyberattack — the problem occurred when it deployed a faulty update to computers running Microsoft Windows.
Microsoft stated, “We have been made aware of an issue impacting Virtual Machines running Windows Client and Windows Server, running the CrowdStrike Falcon agent, which may encounter a bug check (BSOD) and get stuck in a restarting state.”
Microsoft Azure released a fix for this issue. For detailed instructions, visit: https://azure.status.microsoft/en-gb/status
Many users have reported success by repeatedly restarting their VMs. Although it may take multiple attempts (as many as 15 in some cases), this has proven to be an effective troubleshooting step. You can restart your VMs through the Azure Portal or using the Azure CLI:
If you have backups from before 19:00 UTC on July 18th, restoring from these backups is a reliable solution. Here’s how you can do it if you are using Azure Backup:
Another option is to repair the OS disk by attaching it to a repair VM. This allows you to delete the problematic file directly. Here are the steps:
For detailed instructions on repairing the OS disk, refer to: Troubleshoot a Windows VM
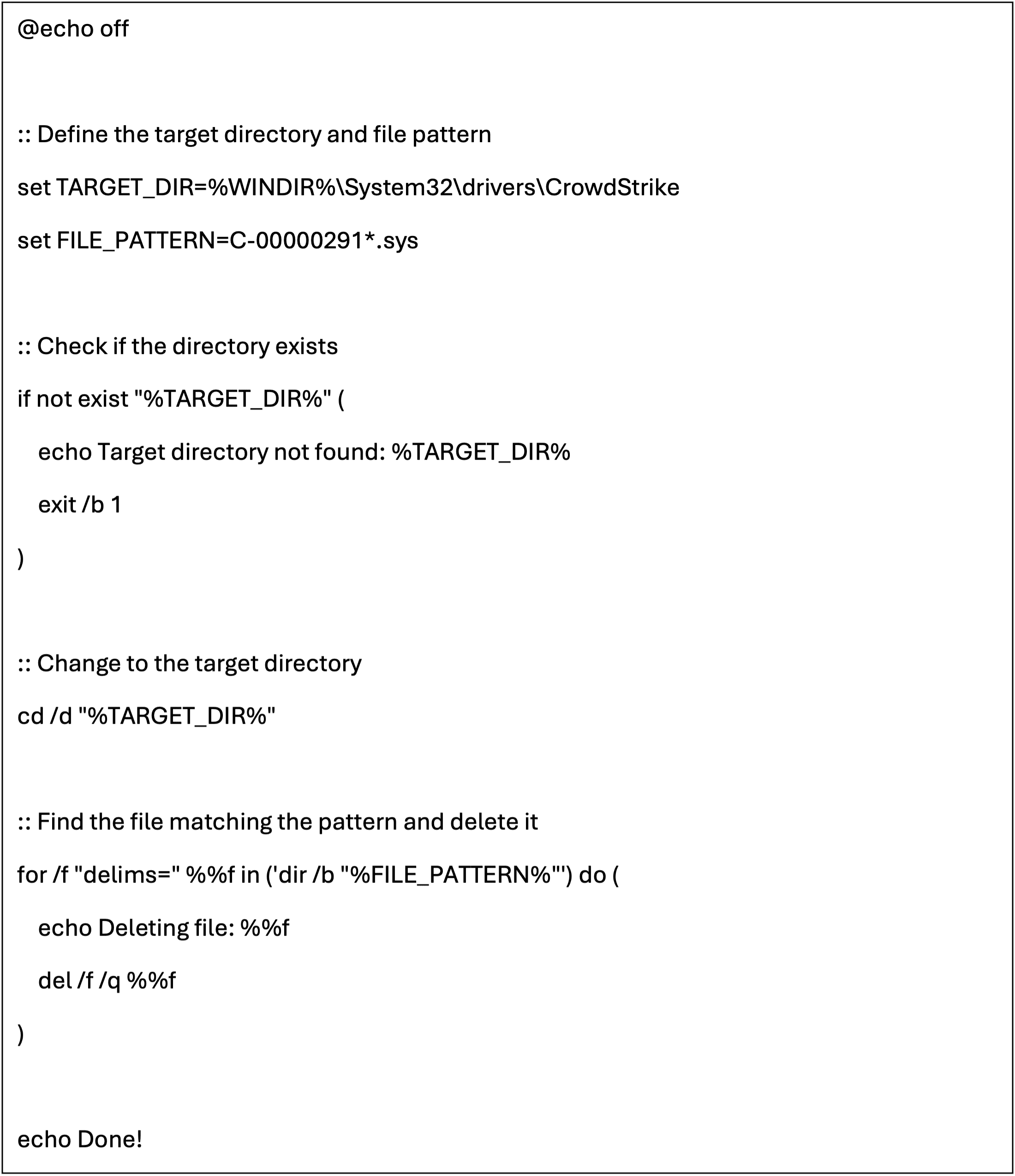
This script automatically finds and removes the problematic .sys file on the host. This script can be put on a USB drive and executed with administrative privileges for ease of use across multiple systems.
The affected update has been pulled by CrowdStrike. Customers that are continuing to experience issues should reach out to CrowdStrike for additional assistance.
Microsoft is continuing to investigate additional mitigation options for customers and will share more information as it becomes known. For current updates, visit: https://azure.status.microsoft/en-gb/status
In this webinar, we’ll explore the dynamic realm of Teaching Digital Natives. Join us to delve into a comprehensive cybersecurity program designed to equip educators with effective strategies, compelling content, and inspiration for both summer camps and middle school courses.
In this webinar, we’ll explore the dynamic realm of Teaching Digital Natives. Join us to delve into a comprehensive cybersecurity program designed to equip educators with effective strategies, compelling content, and inspiration for both summer camps and middle school courses.
The Virtual Internship and Varied Innovative Demonstrations (VIVID) Coalition, comprised of the University of Alabama in Huntsville, Augusta University, University of Arizona, and Florida International University, is excited to announce the 2024 VIVID Cyber Competition.
This competition is an opportunity for students at CAE institutions to strengthen their resumes and showcase their skills in front of U.S. government practitioners.
Teams of five will compete in the virtual cyber competition on March 11-14, 2024. The top 15 teams will be invited to the CAE Annual Colloquium for the top prize and title of “Overlord Champion”.

The hubris of mankind knows no end. How a group of academics think creating machine intelligence is a good thing is beyond belief. The danger of artificial intelligence is well known. Just look at the Forbes article[1] that tells us the risks or even Scientific American[2] which describes the menace of our digital overlords. They even had the audacity to call it “Overlord”; we must stop them!
Fortunately for us, a member of the AU research team that created this monstrosity sees the danger and has told us there is a hidden backdoor to their system that allows remote access. It’s great having an insider that shares our beliefs! Additionally, the creators were at least smart enough to build in an “off switch” but it is protected by an authentication system that needs a digital key. With this knowledge, we can enter the Overlord system and steal the key. Once we have it, we can shut down this monstrosity. Unfortunately, our inside person does not have the credentials to get to the key, so we must break into their system.

Our incident response tasks:
Apex University (AU) announces their new artificial intelligence (AI) research system, Overlord! Professor Rosie Meebs, head of the project, declares “this is a new generation of AI that will reach heights never reached before. Our new code is faster and learns better than anything in existence. We project that in less than 8 months, Overlord will reach singularity and be a true intelligence. We expect once that happens, our AI will be able to solve any number of problems from creating fusion to solving the climate change crisis. Any negative comments are just jealousy, and we know there will be no problems once Overlord comes online. We will turn on Overlord on 1 March 2024 and change the world!”

Our tasks:
You and your team are lucky enough to gain experience at Apex University’s (AU) Security Operations Center (SOC). For the last semester you’ve been working three days a week learning the job roles in SOC and expanding your cybersecurity knowledge. While today is usually not a workday, the SOC director called all of you to work and explained the university network was under attack and all the full-time analysts were swamped. The director needs you to work within the network and identify any artifacts in the system indicating threat activity and indicators of compromise.
SEC allows students to compete in a purely social engineering experience that is grounded in the social sciences. The competition offers a timely and unique platform for students to learn about social engineering in a hands-on, engaging, and ethical manner. The competition has a different theme each year to demonstrate the relevance of social engineering across various cybersecurity areas, and is open to high school, undergraduate, and graduate students.
This year’s theme, tax scams, is inspired by the IRS’ annual Dirty Dozen list of tax scams for 2023. According to IRS Commissioner Danny Werfel, scammers are “coming up with new ways all the time to try to steal information from taxpayers”. So, what exactly are these ways? Come find out how cybercriminals are using social engineering in employment and tax scams.
No technical experience is required. High school and college students (aged 14+) from all disciplinary backgrounds are welcome!
Orientation date (virtual): Saturday, March 23, time TBD (this is not optional – please hold this date on your calendar)
Competition dates (virtual, these are not optional – please hold these dates on your calendar):
Graduate Level: April 5, 6, 7, times TBD
Undergraduate: April 19, 20, 21, times TBD
High school Level: May 3, 4, 5, times TBD
Closing ceremonies (virtual): Wednesday, May 8, time TBD (this is not optional – please hold this date on your calendar)
Why a ‘pure’ social engineering competition?
There are MANY cybersecurity competitions already in existence (PicoCTF, PlaidCTF, CSAW, UCSB iCTF, US Cyber Challenge, Panoply, CPTC, CCDC, CyberPatriot, Cyber Academy, to name a few). While these are all excellent sources of hands-on training, they are primarily technical in nature and have specific focus areas, such as reverse engineering, hacking, cryptography, and exploitation. They do not emphasize the relevance of the human-socio-psychological aspects of cyberattacks and cybersecurity.
Given that the human factor is increasingly being exploited by cybercriminals, a pure SE competition grounded in the social sciences offers a timely and unique platform for students to learn about this topic in a hands-on, engaging, and ethical manner.
Who can participate?
This event is open to high school, undergraduate, and graduate students. Teams are required (solo entries are not permitted). Team sizes can range from 2-4 members. Members can be from different institutions (schools/colleges), but must be at the same educational level (ex: purely high school students).
When and how can we put our application in?
*Registration deadline is Monday, February 19, 2024 at 12pm ET.

October is #CybersecurityAwarenessMonth – with just a few clicks, you can be on your way to keeping yourself safe online.
Stay tuned throughout the month for valuable tips and best practices for staying safe in the cyber world. ?
Cyber Florida invites state and local law enforcement personnel across the Sunshine State to attend this free, one-day workshop presenting the latest insights, methodologies, and updates related to cybercrime. Funded by a grant from the Federal Emergency Management Agency, this event offers an impressive lineup of experts in various domains of cyber investigations, providing a valuable knowledge-sharing platform for officers and officials keen on enhancing their investigative capabilities in an increasingly digital world.
9:00 - 10:00 am: Open Source Intelligence (OSINT)
Dr. Jordan Howell dives into the world of publicly available data and how it can be harnessed to aid in cyber investigations. Dr. Howell will discuss key tools, techniques, and resources available in the realm of OSINT.
10:15 - 11:15 am: Cybercrime Legal Update
Assistant U.S. Attorney Greg Schiller will provide attendees with the latest updates in the legal landscape surrounding cybercrime, providing a clearer picture of the challenges and opportunities facing law enforcement.
11:45 am - 12:45 pm: Current Forensics Challenges
In this session, veteran criminal investigator Chris Gastardi will address the ongoing challenges forensic experts face in digital investigations and cutting-edge techniques to overcome them.
12:45 - 1:45 pm: Networking Lunch (lunch provided, value less than $50)
1:45 - 2:45 pm: Cryptocurrency Investigations and the Blockchain
Cryptocurrencies present unique challenges in the world of cyber investigations. Larry Nielson, CFE, CTCE, CRC, Financial Crimes Detective at the Palm Beach County Sheriff’s Office, will delve deep into the world of blockchain and shed light on techniques to trace, track, and investigate cryptocurrency-related crimes.
3:00 - 3:45 pm: Dark Web Investigations
The Dark Web remains a mystery to many. Jeff Burke, special agent with the Defense Criminal Investigative Service, will uncover the layers of the Dark Web, providing insights into how to navigate, investigate, and track criminal activities on this hidden part of the internet.
4:00 - 5:00 pm: Cyber Investigations
Retired FBI Supervisory Special Agent Chuck Esposito gives a comprehensive look into the realm of cyber investigations, discussing everything from current threats to mitigation strategies.
